There is an oncoming quantum computing threat to cybersecurity. For decades, the digital world has been built on trust. A trust that lead us to believe our encrypted systems are secure, that private communications remain private, and that financial transactions are protected.
This trust is rooted in mathematics, specifically in problems that are so complex they would take classical computers thousands of years to solve.
However, that foundation is beginning to crack.
Quantum computing, once a theoretical concept confined to academic labs, is rapidly advancing into a real-world technology with the potential to disrupt nearly every industry. Among its most immediate and profound impacts is cybersecurity.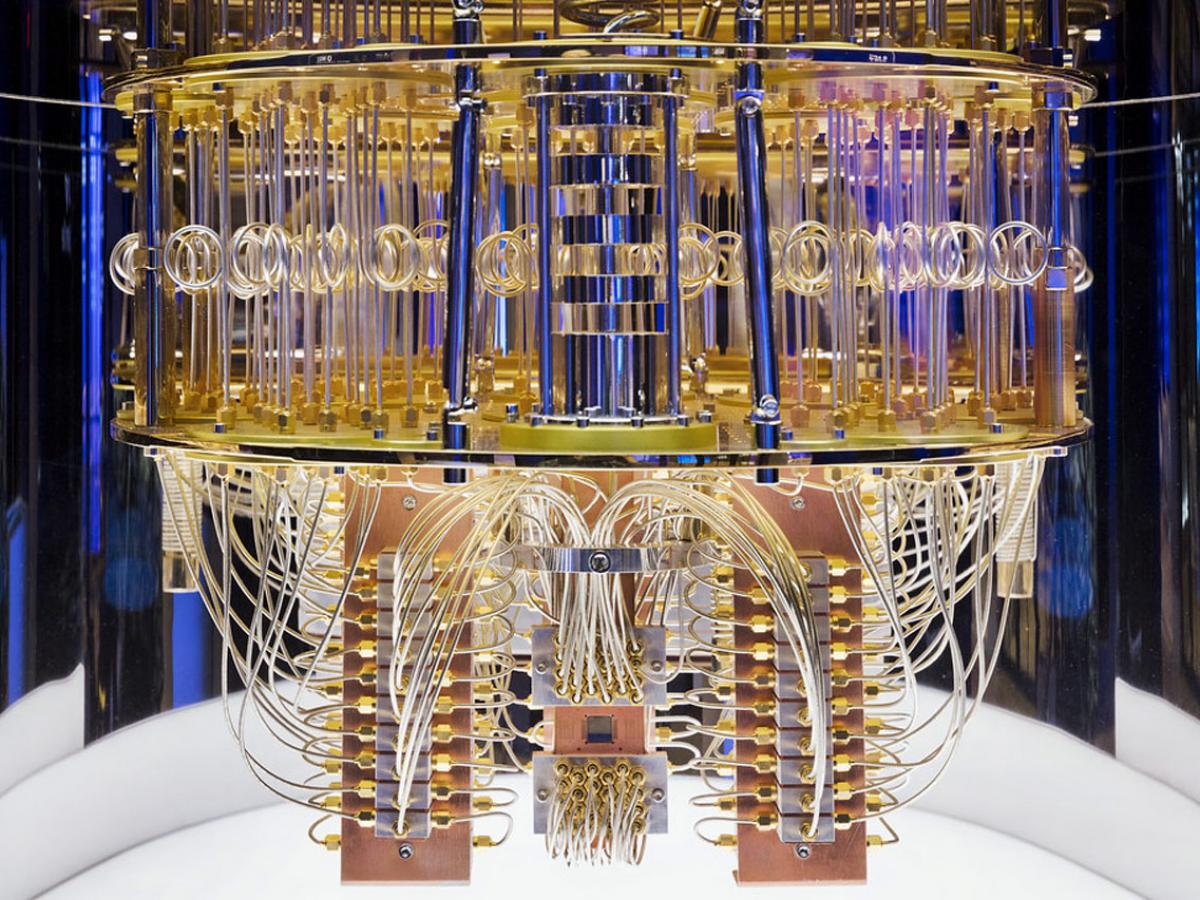
Understanding the Fragile Backbone of Cybersecurity
Experts are no longer debating whether quantum computers will break current encryption standards. They are debating “when” the breakage will occur.
The debate has led to 2030 being “when.”
Modern encryption methods such as RSA and elliptic curve cryptography rely on mathematical asymmetry. It’s easy to create encrypted data using a public key, but extremely difficult to reverse that process without the private key.
This difficulty is what keeps systems secure.
For example, RSA encryption depends on the challenge of factoring very large numbers into their prime components. While this is simple for small numbers, it becomes exponentially harder as numbers grow larger. Classical computers are simply not fast enough to solve these problems efficiently at scale.
This has been the cornerstone of digital security for decades—until quantum computing entered the picture.
What Makes Quantum Computing a Game-Changer
Quantum computers operate on principles fundamentally different from classical machines. Instead of bits, they use qubits, which can exist in multiple states simultaneously. This allows quantum systems to process vast numbers of possibilities in parallel rather than sequentially.
This capability is not just an incremental improvement. It’s a paradigm shift.
Quantum computers leverage phenomena such as superposition and entanglement to solve problems that would be practically impossible for classical systems. Tasks like optimization, molecular simulation, and cryptographic analysis become dramatically faster.
And that includes breaking encryption.
The Encryption Killer: How Quantum Algorithms Change Everything
The primary threat to current cybersecurity systems lies in specialized quantum algorithms designed to exploit mathematical weaknesses in encryption.
Shor’s algorithm is the most widely discussed. It enables quantum computers to factor large numbers exponentially faster than classical algorithms. Since RSA encryption depends on the difficulty of factoring, Shor’s algorithm effectively removes that barrier.
What once took centuries could take hours—or even minutes—with a sufficiently powerful quantum computer.
Another algorithm, Grover’s algorithm, speeds up brute-force searches, reducing the time needed to crack symmetric encryption systems. While not as devastating as Shor’s algorithm, it still weakens existing security models.
Together, these breakthroughs reshape the threat landscape entirely.
“Harvest Now, Decrypt Later”: The Invisible Threat Already in Motion
One of the most alarming aspects of the quantum threat is that it does not require immediate capability to be dangerous.
Attackers can begin collecting encrypted data today—emails, financial records, intellectual property, government communications—and store it until quantum computers become powerful enough to decrypt it.
This strategy is known as “harvest now, decrypt later.”
It means that data you consider secure right now may already be compromised in the future. Sensitive information with long-term value—such as medical records, trade secrets, or national security data—is especially vulnerable.
This is not a future problem. It is a present-day risk.
How Close Are We Really?
There is no universal agreement on exactly when quantum computers will reach the level needed to break encryption, but progress is accelerating faster than many anticipated.
Quantum processors are increasing in qubit count year after year. More importantly, researchers are making strides in reducing error rates and improving stability—two of the biggest challenges in quantum computing.
Major technology companies and governments are investing billions into quantum research. This global race is driving rapid innovation, compressing timelines that once seemed distant.
Some experts believe a cryptographically relevant quantum computer could emerge within the next decade. Others suggest it may take longer, but even the most conservative estimates acknowledge that preparation cannot wait.
Because once the capability exists, the transition window will be extremely narrow.
Industries Facing the Greatest Risk
The impact of quantum-enabled decryption will not be evenly distributed. Some sectors are particularly exposed due to the sensitivity and longevity of their data.
Financial institutions rely heavily on encryption to secure transactions, protect customer data, and maintain trust. A breach at this level could have systemic consequences for the global economy.
Healthcare systems store deeply personal and long-lasting information. Medical records do not lose value over time, making them prime targets for future decryption.
Government and military communications represent some of the highest-value targets. The exposure of classified information could have geopolitical implications.
Technology companies and cloud providers also face enormous risk, as they serve as custodians for vast amounts of user data.
The common thread across these industries is clear: they all depend on encryption that may soon become obsolete.
The Race to Build Quantum-Resistant Security
In response to the growing threat, the cybersecurity community is working to develop new forms of encryption that can withstand quantum attacks. This field is known as post-quantum cryptography.
Unlike current systems, post-quantum algorithms are based on mathematical problems that remain difficult even for quantum computers. These include lattice-based cryptography, hash-based systems, and multivariate equations.
Governments and standards organizations are actively evaluating and standardizing these approaches. The goal is to create encryption systems that can replace or augment current methods before quantum computers become a practical threat.
However, transitioning to new cryptographic standards is not a simple process. It requires updating infrastructure, ensuring compatibility, and maintaining performance across billions of devices.
This is why the timeline matters so much.
Why 2030 Is a Critical Deadline
The year 2030 has become a focal point in discussions about quantum risk—not because it is a guaranteed tipping point, but because it represents a realistic horizon for large-scale disruption.
Replacing global encryption systems is a massive undertaking. It involves software updates, hardware changes, regulatory coordination, and extensive testing.
Even under ideal conditions, this process can take years.
If organizations wait until quantum computers are fully capable, they may not have enough time to respond. This creates a dangerous gap between capability and preparedness.
The safest strategy is to begin transitioning now, while there is still time to do so gradually and securely.
The Hidden Challenge: Legacy Systems
One of the biggest obstacles in preparing for quantum threats is the presence of legacy systems.
Many critical infrastructures—such as power grids, transportation networks, and industrial systems—run on outdated software that cannot be easily upgraded. These systems often rely on encryption methods that will be vulnerable to quantum attacks.
Replacing or updating these systems is costly and complex. In some cases, it may require complete redesigns.
This creates a weak point in global cybersecurity. Even if new systems are secure, legacy infrastructure could remain exposed.
What Businesses Should Be Doing Right Now
Organizations cannot afford to treat quantum computing as a distant concern. The transition to quantum-resistant security must begin well before the threat becomes imminent.
Key actions include assessing current cryptographic dependencies, identifying high-risk data, and developing a migration strategy toward post-quantum solutions.
Businesses should also consider adopting hybrid encryption models that combine classical and quantum-resistant methods. This approach provides an additional layer of protection during the transition period.
Equally important is staying informed. The field of quantum computing is evolving rapidly, and organizations must keep pace with new developments and standards.
Preparation is not a one-time effort—it is an ongoing process.
What This Means for Everyday Users
While much of the discussion around quantum cybersecurity focuses on governments and large corporations, individuals are not immune to the risks.
Personal data, financial information, and private communications are all protected by encryption that could eventually be compromised.
The good news is that most of the responsibility for addressing this threat lies with service providers and technology companies. As they transition to quantum-resistant systems, users will benefit from improved security.
However, awareness still matters. Understanding the risks can help individuals make better decisions about data privacy and digital security.
The Double-Edged Sword of Quantum Innovation
It is important to recognize that quantum computing is not inherently a threat. In fact, it has the potential to drive major advancements across multiple fields.
In medicine, quantum simulations could accelerate drug discovery. In materials science, they could enable the development of stronger and more efficient materials. In artificial intelligence, they could unlock new levels of performance.
But like any powerful technology, quantum computing introduces new risks alongside its benefits.
Cybersecurity is simply the first domain where those risks are becoming visible.
The Global Race
Quantum computing is not just a technological race—it is a geopolitical one.
Countries around the world are investing heavily in quantum research, recognizing its strategic importance. The ability to break encryption could provide a significant advantage in intelligence and cybersecurity.
This creates a new kind of arms race, where the stakes are not measured in weapons, but in information.
The outcome of this race will shape the future of global security.
The Future of Encryption
Looking beyond the immediate challenge, the rise of quantum computing may ultimately lead to a new era of cybersecurity.
Quantum key distribution, for example, uses the principles of quantum mechanics to create theoretically unbreakable encryption. While still in its early stages, this technology could redefine how secure communication is achieved.
In this sense, quantum computing may not just break current systems—it may also inspire the creation of stronger ones.
A Narrow Window to Act
The possibility that quantum computers could break current encryption before 2030 is no longer a fringe concern. It is a credible scenario that demands immediate attention.
The transition to quantum-resistant security will take time, coordination, and significant investment. But the cost of inaction could be far greater.
Cybersecurity has always been a race between defenders and attackers. Quantum computing has the potential to dramatically accelerate that race.
The question is not whether change is coming—it is whether we will be ready when it does.